Operational Technology (OT) systems are responsible for monitoring and managing industrial processes, assets, and equipment within factory floors and other industrial settings. Here are some examples of OT applications in different sectors:
Manufacturing:
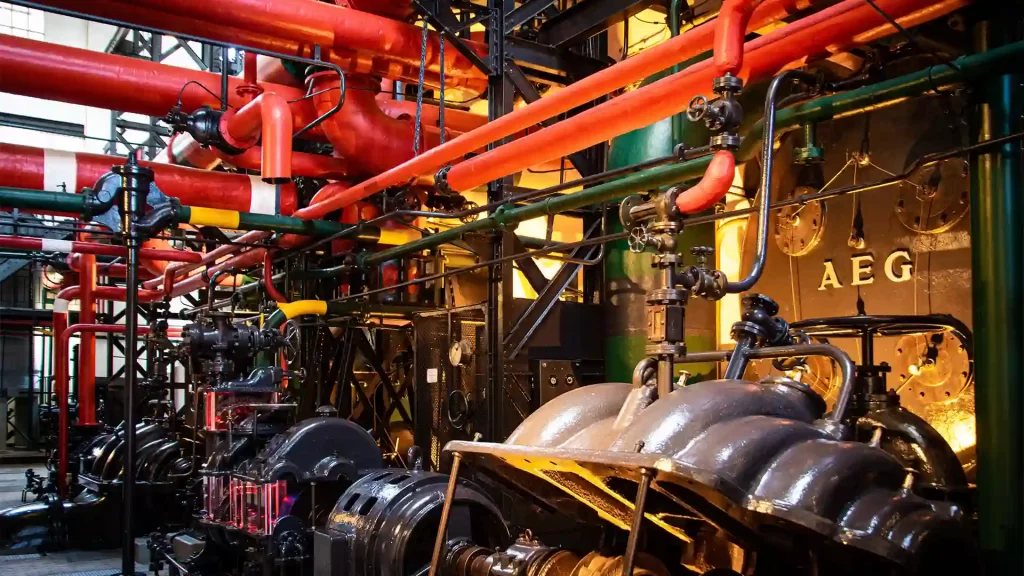
Supervisory Control and Data Acquisition (SCADA) systems: Operational technology is used to manage and control industrial processes, including production, quality control, and equipment maintenance.
Programmable Logic Controllers (PLCs): OT devices used to automate and control machinery and equipment in manufacturing plants.
Oil & Gas:
Remote Monitoring and Control Systems: OT is used to monitor and control oil and gas operations, including drilling, pipeline management, and production facilities.
Distributed Control Systems (DCS): OT systems are used to manage and optimize processes in oil refineries and petrochemical plants.
Safety Instrumented Systems (SIS): Operational Technology is employed to ensure the safe operation of critical processes and equipment in the oil and gas industry.
Infrastructure:
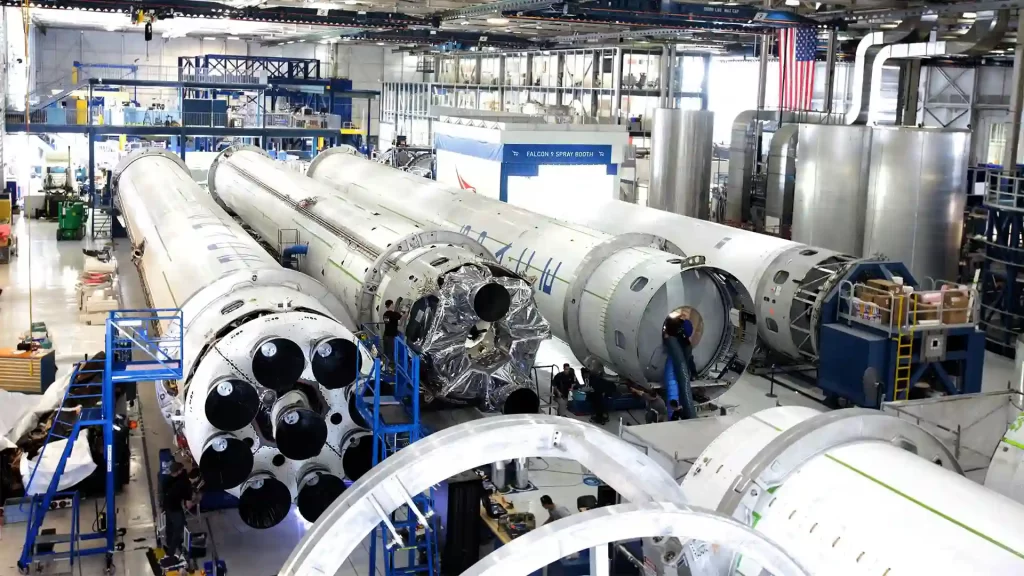
Smart Grid Systems: OT is employed to manage and control electricity generation, distribution, and consumption in utility infrastructures.
Traffic Control Systems: OT is used to monitor and manage traffic flow, signals, and infrastructure for efficient transportation management.
Utilities:
Water and Wastewater Management: operational technology systems monitor and control water treatment and distribution systems, as well as wastewater collection and treatment processes.
Power Generation and Distribution: OT is used in power plants to manage and control electricity generation, transmission, and distribution.
Renewable Energy Systems: OT plays a crucial role in managing and optimizing renewable energy sources like solar and wind farms.
In today’s times the integration of OT and IT networks has become increasingly common, allowing for improved operational efficiency and data analysis. However, this integration also introduces potential risks. By connecting OT and IT systems, a hacker could exploit vulnerabilities in one system to gain unauthorized access to the other. For example, a cybercriminal could breach the IT network and use it as a pathway to infiltrate and disrupt the operational technology system, potentially causing significant damage and operational disruptions.
To mitigate these risks, organizations must implement robust cybersecurity measures that consider the unique characteristics of both OT and IT environments. This includes implementing strong access controls, network segmentation, intrusion detection systems, and regular patching and updates. Additionally, organizations should prioritize security awareness and training for employees who interact with both OT and IT systems to ensure they are equipped to identify and respond to potential threats.
By understanding the risks associated with integrating OT and IT networks and implementing appropriate security measures, organizations can enhance their overall cybersecurity posture and minimize the potential for cyber-attacks that exploit vulnerabilities across both systems.
